-
Resources
- Forums
-
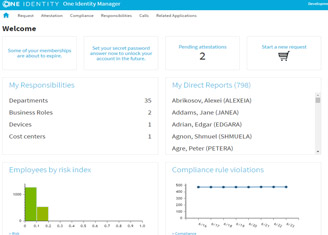
Bringing accountability to European retailer
 02:47
02:47
See how dm-drogerie markt, with 60,000 employees and 3,500-plus stores across central and eastern Europe, saves money and gains efficiency.
Related videos
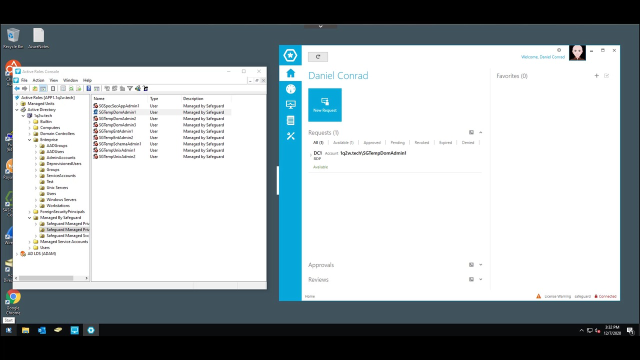
Making Zero Trust Real with Active Directory
What is Zero Trust and how can it be applied in an Active Directory world? See how transcends solutions and is a change in how security is perceived. Watch this video to learn more.
Duration: 29:14